The smart Trick of Sniper Africa That Nobody is Talking About
The smart Trick of Sniper Africa That Nobody is Talking About
Blog Article
Things about Sniper Africa
Table of Contents4 Easy Facts About Sniper Africa ShownExcitement About Sniper AfricaNot known Facts About Sniper AfricaThe Sniper Africa Statements8 Easy Facts About Sniper Africa ShownThe 6-Minute Rule for Sniper AfricaNot known Factual Statements About Sniper Africa

This can be a certain system, a network area, or a theory set off by an announced susceptability or patch, info about a zero-day manipulate, an anomaly within the protection data set, or a request from somewhere else in the organization. Once a trigger is identified, the hunting initiatives are concentrated on proactively looking for abnormalities that either show or disprove the theory.
The Basic Principles Of Sniper Africa

This process may involve making use of automated tools and queries, along with hands-on analysis and correlation of information. Unstructured searching, additionally referred to as exploratory hunting, is a more flexible strategy to risk hunting that does not count on predefined requirements or hypotheses. Rather, risk seekers utilize their knowledge and instinct to look for potential dangers or susceptabilities within an organization's network or systems, frequently concentrating on areas that are viewed as high-risk or have a background of security occurrences.
In this situational method, danger hunters use hazard knowledge, together with other appropriate data and contextual info regarding the entities on the network, to recognize potential hazards or vulnerabilities connected with the situation. This might include the usage of both structured and disorganized searching methods, as well as partnership with various other stakeholders within the organization, such as IT, lawful, or service teams.
4 Easy Facts About Sniper Africa Described
(https://issuu.com/sn1perafrica)You can input and search on threat knowledge such as IoCs, IP addresses, hash values, and domain. This procedure can be incorporated with see this your protection info and event administration (SIEM) and risk knowledge tools, which utilize the intelligence to search for threats. Another great source of knowledge is the host or network artifacts supplied by computer emergency response teams (CERTs) or details sharing and evaluation centers (ISAC), which may allow you to export computerized notifies or share key info concerning new strikes seen in other companies.
The initial step is to recognize appropriate teams and malware strikes by leveraging global discovery playbooks. This strategy frequently aligns with danger frameworks such as the MITRE ATT&CKTM structure. Below are the actions that are most usually included in the procedure: Use IoAs and TTPs to determine threat stars. The hunter examines the domain name, environment, and attack habits to develop a hypothesis that straightens with ATT&CK.
The goal is situating, identifying, and after that separating the hazard to avoid spread or spreading. The crossbreed hazard searching method integrates all of the above techniques, allowing safety analysts to customize the quest. It usually includes industry-based hunting with situational awareness, incorporated with defined hunting needs. The search can be personalized utilizing information concerning geopolitical concerns.
The Sniper Africa Ideas
When operating in a safety operations center (SOC), threat hunters report to the SOC manager. Some important skills for an excellent hazard hunter are: It is essential for hazard hunters to be able to communicate both verbally and in creating with excellent clearness regarding their activities, from investigation completely with to searchings for and referrals for removal.
Information breaches and cyberattacks price organizations numerous bucks annually. These suggestions can aid your company better spot these dangers: Threat hunters need to filter via strange tasks and recognize the actual dangers, so it is essential to recognize what the normal functional tasks of the company are. To accomplish this, the risk hunting team works together with vital workers both within and outside of IT to collect beneficial info and insights.
Getting My Sniper Africa To Work
This procedure can be automated making use of a modern technology like UEBA, which can show normal operation problems for an atmosphere, and the users and makers within it. Danger seekers use this technique, borrowed from the armed forces, in cyber warfare.
Identify the correct training course of action according to the occurrence standing. A danger hunting group ought to have sufficient of the following: a hazard hunting team that includes, at minimum, one knowledgeable cyber risk seeker a fundamental threat searching infrastructure that collects and arranges safety and security cases and events software application created to identify anomalies and track down aggressors Hazard seekers use options and devices to discover suspicious tasks.
How Sniper Africa can Save You Time, Stress, and Money.
Unlike automated risk discovery systems, hazard hunting depends greatly on human intuition, matched by innovative tools. The stakes are high: An effective cyberattack can lead to data violations, financial losses, and reputational damage. Threat-hunting tools give protection teams with the understandings and abilities needed to stay one step in advance of enemies.
See This Report on Sniper Africa
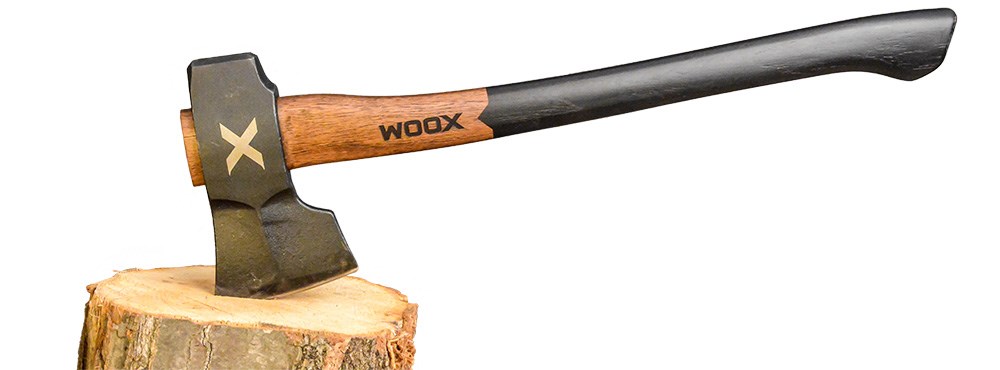
Here are the characteristics of efficient threat-hunting tools: Continual surveillance of network traffic, endpoints, and logs. Smooth compatibility with existing safety infrastructure. hunting jacket.
Report this page